


In modern military operations, assured positioning, navigation, and timing (PNT) capabilities are critical. Spirent Federal specializes in simulating realistic, mission-representative navigation warfare (NAVWAR) environments to help defense partners validate and harden their systems against a wide spectrum of PNT threats.

From GPS jamming and spoofing to advanced multi-domain threats, warfighters face a growing array of challenges in maintaining reliable navigation. Simulated NAVWAR environments allow PNT systems to be evaluated and hardened under the same contested and degraded conditions they’ll face in theater—without the operational risk.

PNT X is Spirent’s sixth‑generation PNT simulation system. Purpose-built for mission-critical environments, it simplifies comprehensive NAVWAR testing to accelerate deployment of resilient PNT solutions to warfighters.
Powerful Performance: PNT X delivers uncompromised signal generation across GNSS, encrypted miliary signals, LEO constellations, and custom waveforms—even in the most demanding test cases.
Unrivaled Realism: Advanced 3D terrain modeling and dynamic signal propagation effects with I/Q spatial awareness replicate real-world NAVWAR threats with precision.
Technological Simplicity: One platform handles it all—reducing hardware complexity, streamlining hardware-in-the-loop integration, and simplifying CRPA testing with intuitive controls.
Read Simulating NAVWAR eBook to learn more.

Anti-jam antennas such as controlled reception pattern antenna (CRPA) systems are critical to winning in NAVWAR, but accurate CRPA testing demands tightly synchronized, phase-coherent signal generation—something only PNT X delivers at scale. With its phase-aligned wavefront simulation and support for high-element arrays (20+ elements), PNT X enables true dynamic CRPA testing in both conducted and over-the-air (OTA) configurations. Its software-defined, purpose-built architecture makes it the gold standard for mission-representative anti-jam antenna validation.
Watch the April 2025 webinar on CRPA testing
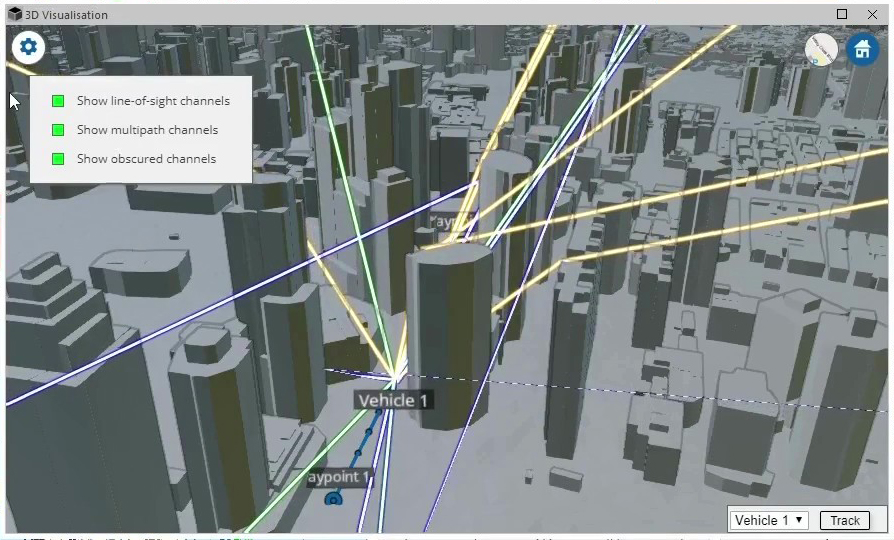
PNT X 3D Terrain Modeling with multipath and obscuration effects on truth, spoof, and jamming signals
PNT X isn’t just a simulator—it’s a all-in-one test platform that sets a new benchmark for realism, precision, and adaptability. From advanced CRPA testing to dynamic spoofing and jamming scenarios, PNT X gives you the confidence to develop, integrate, and deploy systems that can withstand the evolving NAVWAR threat landscape.
Ready to see it in action? Contact us to schedule a demo.

Next-Gen NAVWAR 3D Simulation: Gaining Tactical Advantage
What you’ll learn During this webinar, the experts will delve into several key topics, providing you with a robust understanding of the factors that influence GNSS performance in jamming environments. Key discussion points Signal Propagation Effects. Explore how different signal propagation characteristics—such as obscuration, diffraction, and open sky conditions—impact GNSS performance under jamming conditions. Jamming […]
View Webinar
What is a CRPA (Controlled Reception Pattern Antenna)?
You may sometimes see CRPA referred to as either controlled reception pattern antenna or controlled radiation pattern antenna. The terms are often used interchangeably, and both refer to the same essential concept: an antenna system that dynamically adjusts how it receives GNSS signals to defend against interference and protect navigation performance. In simple terms, a […]
Read Blog
Build ultra-realistic PNT test scenarios with 3D terrain modeling in PNT X
Developers of positioning, navigation and timing (PNT) equipment usually have to sacrifice realism when testing with simulators in the lab. No simulator can ever replicate the true richness of the real-world environment, making field testing an important part of the development cycle. But it’s now possible to get closer to real-world conditions in the lab […]
Read Blog